Keep your communications in private. Our e-mails is ecnrypted, our company is based in Silicon Valley, California, and our se servers in Amsterdam, Netherlands.

E-mail Encrypted Plans
Choose an ideal plan for you or your business.
1 @hacker.engineer
+ 50 MB
$99.99/yr
(2/mo discount)
Top Features
HACKER<#4+! Prime Features UNLOCKED
E-mail Over VPN
PGP Encryption Keys
Outside USA (Amsterdam)
No Logs-No Tracking
TLS-SSL AES-256-GCM
TOR Onion
Triple Encryption
SMTPS-IMAPS Encrypted
Windows-MAC-Linux-BSD Compatibility
Iphone-Android Compatibility
DNSSEC-SPF-DMAC-DKIM Filters
Outlook-Thunderbird-K9 Compatibility
Anti-Virus-Spam-Malware
STANDARD Plan is a great place to start for your first low-traffic communications`.
It's easy to update in the future as you want.
Features Included as standard on all plans
Our Email plans include the following great features to help you get the most.
By default all plans come with our greate inspired email @hacker.engineer.
To you have access to your e-mail you need to be connected to our VPN, and this is FREE.
At the moment you create yout account our system will create your PGP Private and Public Keys! You are ready to go!
If for some reason you are been blocked to use VPN, you can use our hidden TOR E-mail Service Network.
Your account is protected with many technologies to keep you out from virus, malwares, spammers, ...
To sign a message, the sender uses their private key to create a digital signature. The recipient can then use the sender's public key to verify the signature and confirm the authenticity of the message
We're here to help you with whatever you need.
E-mail Encrypted Plans
Choose an ideal plan for you or your business.
1 @hacker.engineer
+ 100 MB
$149.99/yr
(2/mo discount)
Top Features
E-mail Over VPN
PGP Encryption Keys
Outside USA (Amsterdam)
No Logs-No Tracking
TLS-SSL AES-256-GCM
TOR Onion
Triple Encryption
SMTPS-IMAPS Encrypted
Windows-MAC-Linux-BSD Compatibility
Iphone-Android Compatibility
DNSSEC-SPF-DMAC-DKIM Filters
Outlook-Thunderbird-K9 Compatibility
Anti-Virus-Spam-Malware
1 @hacker.engineer
+ 300 MB
$199.99/yr
(2/mo discount)
Top Features
E-mail Over VPN
Encrypted E-mails
Outside USA (Amsterdam)
No Logs-No Tracking
TLS-SSL AES-256-GCM
TOR Onion
Triple Encryption
SMTPS-IMAPS Encrypted
Windows-MAC-Linux-BSD Compatibility
Iphone-Android Compatibility
Firewall Protection
DNSSEC-SPF-DMAC-DKIM Filters
Outlook-Thunderbird-K9 Compatibility
DNS Leak Protection
Anonymous Hidden IP
Anti-Virus-Spam-Malware
No Censorship
PGP Encryption
E-mail @hacker Over VPN Only
E-mail @engineer Over VPN Only
E-mail @me Over VPN Only
Other E-mail Domains (alias)
Messenger XMPP
VOIP
Video Conference
Hacker News
Web Proxy Encrypted
Encrypted Forward E-mails
BACKUP
1 @hacker.engineer
2 Alias
+ 500 MB
$249.99/yr
(2/mo discount)
Top Features
E-mail Over VPN
Encrypted E-mails
Outside USA (Amsterdam)
No Logs-No Tracking
TLS-SSL AES-256-GCM
TOR Onion
Triple Encryption
SMTPS-IMAPS Encrypted
Windows-MAC-Linux-BSD Compatibility
Iphone-Android Compatibility
Firewall Protection
DNSSEC-SPF-DMAC-DKIM Filters
Outlook-Thunderbird-K9 Compatibility
DNS Leak Protection
Anonymous Hidden IP
Anti-Virus-Spam-Malware
No Censorship
PGP Encryption
E-mail @hacker Over VPN Only
E-mail @engineer Over VPN Only
E-mail @me Over VPN Only
Other E-mail Domains (alias)
Messenger XMPP
VOIP
Video Conference
Hacker News
Web Proxy Encrypted
Encrypted Forward E-mails
BACKUP
1 @hacker.engineer
4 Alias
+ 1GB MB
+ PROXY + VPN + SITE
$499.99/yr
(2/mo discount)
Top Features
E-mail Over VPN
Encrypted E-mails
Outside USA (Amsterdam)
No Logs-No Tracking
TLS-SSL AES-256-GCM
TOR Onion
Triple Encryption
SMTPS-IMAPS Encrypted
Windows-MAC-Linux-BSD Compatibility
Iphone-Android Compatibility
Firewall Protection
DNSSEC-SPF-DMAC-DKIM Filters
Outlook-Thunderbird-K9 Compatibility
DNS Leak Protection
Anonymous Hidden IP
Anti-Virus-Spam-Malware
No Censorship
PGP Encryption
E-mail @hacker Over VPN Only
E-mail @engineer Over VPN Only
E-mail @me Over VPN Only
Other E-mail Domains (alias)
Messenger XMPP
VOIP
Video Conference
Hacker News
Web Proxy Encrypted
Encrypted Forward E-mails
BACKUP
Our Solutions, but Not Limeted
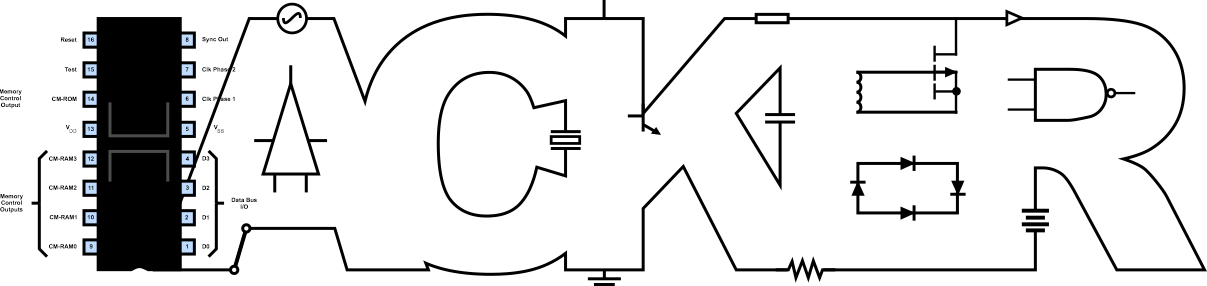
Some of our technologies and solutions









Our Email is protected by multiple layers of security using the most advanced and secure technologies on this days.
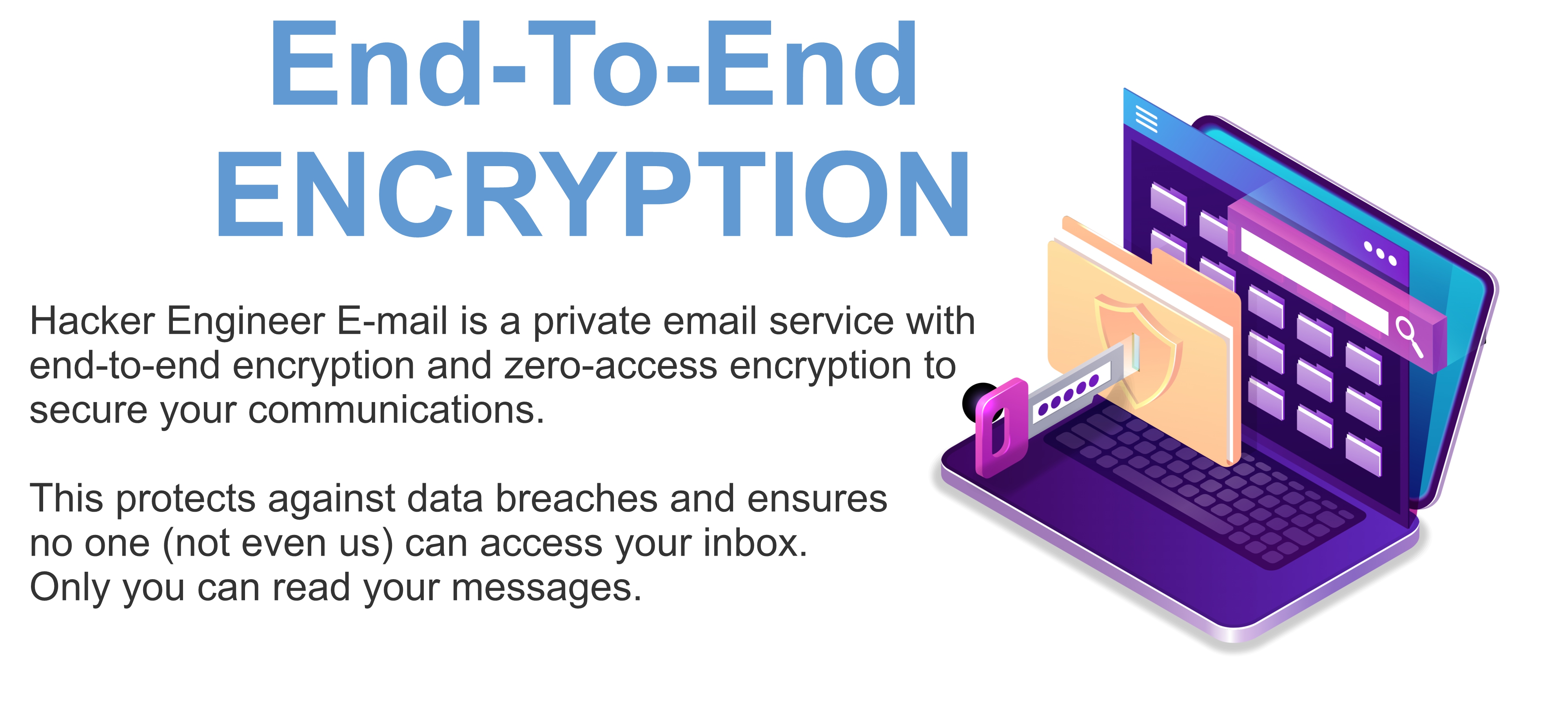
Strong EncryptionWe use end-to-end encryption and zero-access encryption to ensure that only you can read your emails. We cannot read or give anyone else access to your emails. And this encryption happens automatically.
End-to-end EncryptionEmails are encrypted at all times, so we can never access your messages. The content of your emails is encrypted on your device before being sent to our servers, meaning only you and your intended recipient can decrypt it.
You can quickly send end-to-end encrypted emails to any email address, not just Hacker Engineering accounts.
Zero-access encryptionZero-access architecture means we can never access your emails. Emails from other service providers are instantly encrypted on our servers using your public key, meaning we do not have the technical ability to decrypt your messages.
Fun and Profit
Choose the best E-mails domain to express your online personality.
Are you a Hacker? Are you a Engineer? Or are you a hacker and engineer?
Are you a Red Team? Are you a malware hunter? Are you a biologist? Are you a low level programmer? Bug hunter?
Are you feel like a CyberPunk?
Are you the best of the best engineer? Like the engineer boss? The patron?
Are you a very bad engineer? Like to burn?
Are you a radio frequency engineer? Are you like radio stuffs? Are you a radio amateur? Like to broadcast?
Are you a reverse engineer? A bug bounter? Like to reverse things? Then you need a .re email.
You like to have a fun e-mail? We are here for fun and profit! :)
You like to have a fun e-mail? We are here for fun and profit! :)
Do you thinkg this host defines your online personality? Want to have an email like you@cyberpunk.hacker.enginner?
Do you thinkg this host defines your online personality? Want to have an email like you@phreak.hacker.enginner?
Do you thinkg this crazy host defines your online personality? Want to have an email like you@reverse.hacker.enginner?
Our private engineer domain! Only works under the VPN! Good to have a 100% of secure communications with your hackers engineers friends! 100% hidden from the world! No .com or .anything! Your e-mail is you@ENGINEER
Our private hacker domain! Only works under the VPN! Good to have a 100% of secure communications with your hackers engineers friends! 100% hidden from the world! No .com or .anything! Your e-mail is you@HACKER
Our private me domain! Only works under the VPN! Good to have a 100% of secure communications with your hackers engineers friends! 100% hidden from the world! No .com or .anything! Your e-mail is you@i
We are connected to the TOR Network
Below a list of benefits
Tor is free, open-source software for enabling anonymous communication. When you connect to the internet via Tor, your internet is routed through a worldwide, volunteer network of relays that conceal your location and activity from anyone trying to monitor you.
Why use Tor?Using Tor to access Proton is optional, but in some situations it may bring additional security benefits. Instructions on how to use our Tor encrypted email or Tor encrypted file storage access can be found here(new window). More information about how Proton uses Tor to protect your privacy can be found here(new window).
Our Tor Hostfymtsmpy6nt5nsgamwc6xsto545fllm6waawua7wsaqiwgger5kzh7ad.onion
Keep in mindUsing Tor does come with some downsides. Tor connections typically deliver much slower and less reliable performance than a standard internet connection.
Even without using Tor, Our's services are secured with end-to-end encryption, secure authentication (SRP), and optional two-factor authentication. Most people will not need to use our Tor encrypted email or Tor encrypted file storage access. However, if you are an activist in a sensitive situation, our onion site provides an extra layer of anonymity and protection.
Plataforms CompatibilityTor is available for all operational system and all phones.
Migrate your Inbox
Make us your default e-mail and domain provider
Why use Hacker Engineering solutions?
See a list of reasons
People are the weakest link in any security system, which is why we have added several layers of defense against social engineering attacks and human error. Best of all, these features don’t require any extra steps. Your inbox is secured by default.
Protect yourself against mass surveillance from government agencies like the NSA by using a private email provider like we. We don’t have access to your email messages, so we can’t hand them over to any government agency.
Unlike other email providers, we don’t hold the decryption keys for your emails. This means that your messages can’t be decrypted, even if our servers were hacked. If you use Proton Mail, you’re less vulnerable to email server hacks like the Microsoft Exchange hack of 2021.
We are funded by subscriptions to our paid plans, not by invading your privacy and serving you advertisements. Unlike other email services, we have no motivation to use your data to deliver surveillance-based advertising in your inbox.